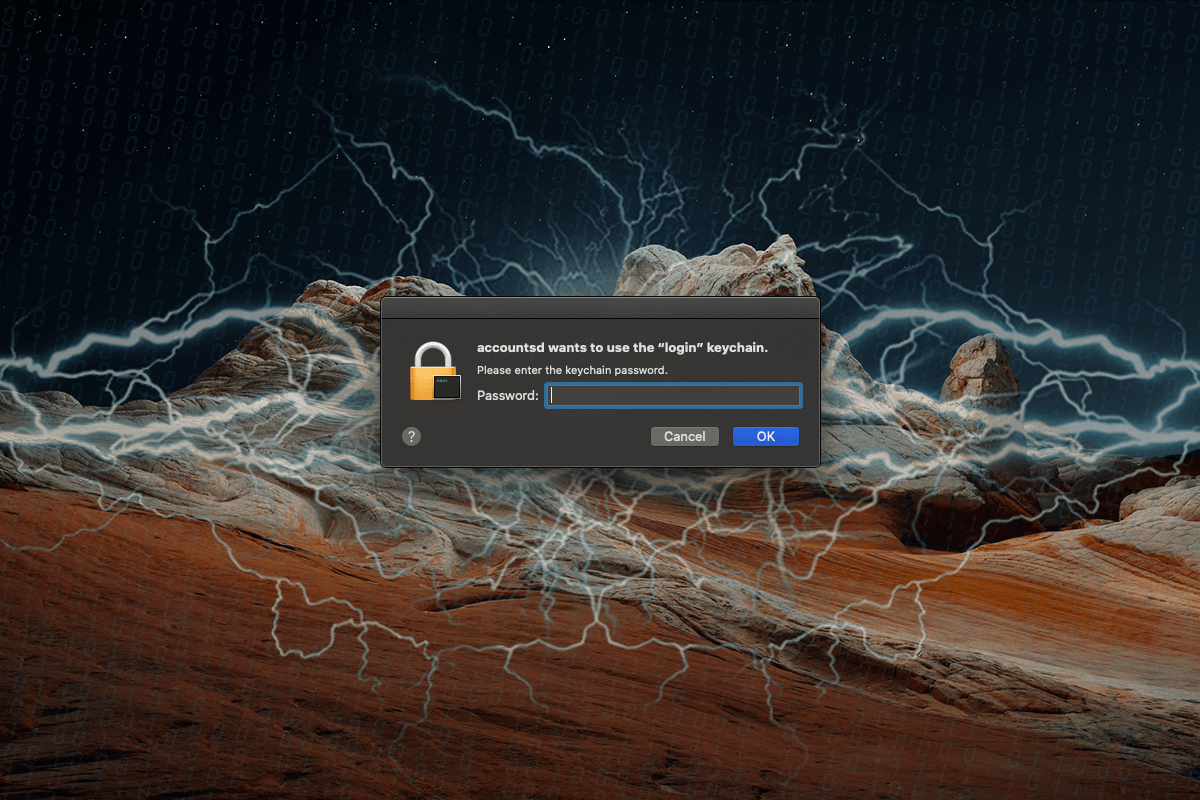
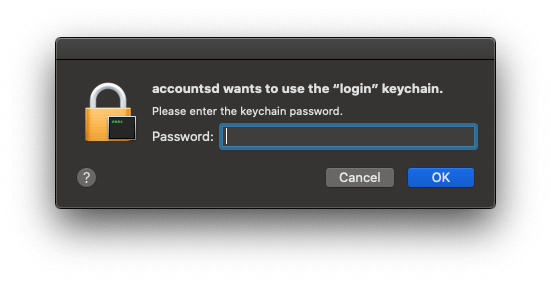
Here is how to stop an influx of pop-up alerts on Mac saying “accountsd wants to use the login keychain”, which can be a sign of misconfiguration or malware.
Update: April 2024
What is the “accountsd wants to use the login keychain” alert?
With the ubiquity of potentially unwanted or outright harmful Mac applications in the wild, there are plenty of hypothetical situations that can undermine or ruin the user experience through annoying pop-ups within or outside a web browser. That being said, warnings that are caused by bugs or inconsistencies at the level of the operating system seem to be the lesser of two evils, but they are equally frustrating. To top it off, sometimes it’s problematic to differentiate between malicious or benign catalysts for such activity, which hampers the process of accurately diagnosing the root cause. This ambiguity applies to the issue where pop-up alerts saying “accountsd wants to use the “login” keychain” are repeatedly displayed on a Mac computer.
Let’s start with the non-malicious facet of this problem. For clarity’s sake, it’s worth diving into the essence of the accountsd entity first. It is a system service geared toward ensuring that the installed applications and the Mac user’s accounts are acting in concert. This bilateral harmony is a prerequisite for seamlessly accessing the native and third-party utilities without the need to enter authentication details off and on. To make this awesomeness happen, the user should head to Internet Accounts under System Preferences and enroll the frequently used services there. On a side note, the iCloud account is added to this list automatically. At some point, though, this synchronization may stop functioning the way it should.
The “accountsd wants to use the login keychain” pop-up problem often appears after macOS updates – either major or supplementary ones. The possible correlation between these two occurrences is as follows: system tweaks may cause this keychain to be locked, although they shouldn’t. When this drag kicks in, the workaround is to open the “Keychain Access” app from the Mac’s “Utilities” interface, right-click the “login” entry in the sidebar, choose “Change Settings for Keychain login”, and deselect the “Lock when sleeping” option if the box next to it is checked. Also, consider disabling the “Lock after” feature or enter a period of inactivity longer than the default five minutes.
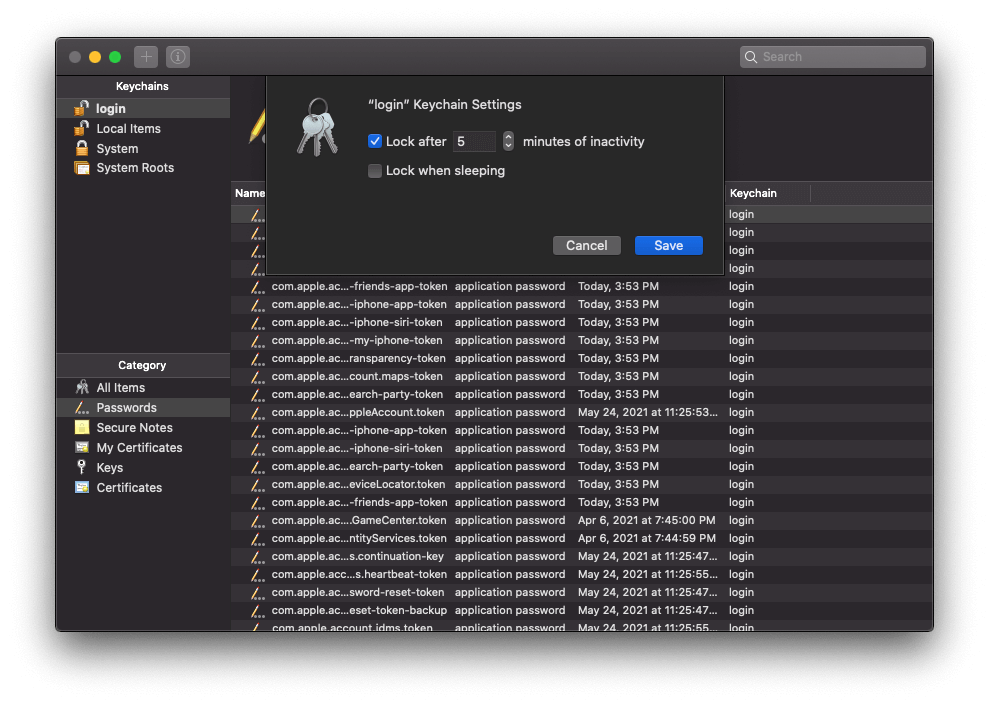
Another likely scenario where the “accountsd wants to use the login keychain” pop-ups start flooding the system stems from a change of the macOS user account credentials. Ideally, the new password should take effect across all the services and applications without any manual action. However, this isn’t always the case, and the authentication data for the high-level “login” keychain and for the system might not match. If so, the easy fix is to make sure that the keychain and the system are using the same password. To do it, open the “Keychain Access” screen once again, right-click “login”, and select “Change Password for Keychain ‘login’” in the context menu. Enter and confirm the new password to bring credentials back into sync.
The issue isn’t isolated to accountsd
In many cases, the frustrating bug in question co-occurs with similar pop-up activity involving a handful of other system processes. No matter if the user enters the Keychain password or hits “Cancel” during login, noxious alerts that mention other daemons just cycle through in a specific sequence non-stop and call forth a spike in CPU and memory usage. Below is a brief overview of these commonly encountered dialogs.
- assistantd wants to use the “login” keychain. The daemon named assistantd is part of Siri, Apple’s famous voice-enabled app. To do its thing, this functionality may need to use Contacts and other sensitive data on a Mac. This explains why it requires access to Keychain.
- CallHistoryPluginHelper wants to use the “login” keychain. Another Keychain-thirsty process on the list, CallHistoryPluginHelper is part of FaceTime, the video calls feature built into macOS. It can be found at the following path: /System/Library/PrivateFrameworks/CallHistory.framework/Support/CallHistoryPluginHelper. When a glitch occurs, this entity will be repeatedly asking for Keychain password.
- callservicesd wants to use the “login” keychain. This daemon needs access to Keychain for a reason, too. Tasked with monitoring call state on your Mac, it has close ties with such apps as FaceTime, Messages, Contacts, and third-party video conferencing programs like Zoom and Skype. All of these store and manage personal information.
- cloudd wants to use the “login” keychain. The operating system uses the cloudd process to sync documents and files stored on your Mac with iCloud. Again, since it handles sensitive details, it needs appropriate access. By the way, this object is often also associated with pop-ups that say, “cloudd wants to use the “Local Items” keychain”.
- CommCenter wants to use the “login” keychain. CommCenter manages network connectivity on Mac machines and iOS devices. As such, it also underlies the calling and messaging functionality, both of which hinge on personal data handled by Keychain.
- com.apple.icloudhelper wants to use the “login” keychain. Judging by the name, this is a system component (probably a LaunchAgent) that participates in exchanging data between your Mac and iCloud. With confidential information being transmitted along the way, this object may require access to the appropriate secret database in the system.
- identityservicesd wants to use the “login” keychain. The Identity Services Daemon kicks in when the system deals with third-party credentials. Instances of handling such highly sensitive data and Keychain access go hand in hand.
- ScopedBookmarkAgent wants to use the “login” keychain. The entity mentioned in this alert is related to application sandboxing and is mostly a part of developers’ vocabulary. It’s used to invoke a “security-scoped bookmark” mechanism that provides a sandboxed app with persistent access to file-system repositories beyond its original environment.
- sharingd wants to use the “login” keychain. This daemon is at the core of quite a few hugely popular macOS features that enable file sharing across Apple devices, including Handoff, AirDrop, and Instant Hotspot. Naturally, most of these workflows are based on user permissions and hence may need access to system Keychain.
- Spotlight wants to use the “login” keychain. The functionality of Apple’s proprietary desktop search feature would be half-baked if it couldn’t use Keychain information, as this affects the accuracy of some results. Ideally, it has the right access by default, but sometimes things can get finicky.
A misconfiguration or something else?
Blaming the pop-up activity on a system glitch is the correct train of thought in most cases, but there is an extra shade of this problem most users are clueless about. Some strains of Mac malware masquerade themselves as legitimate system services, and a few are even capable of riddling regular processes with toxic components to slip under the radar. Things get worse if this impersonation trick is aimed at accessing the victim’s keychains, which is a source of highly sensitive information that might fuel identity theft and virus distribution campaigns. Therefore, if the “accountsd wants to use the login keychain” and similar alerts are recurrently popping up on a Mac, one of the important remediation steps is to check the system for harmful code and remove whatever is detected.
“Accountsd wants to use the login keychain” virus alert manual removal for Mac
The steps listed below will walk you through the removal of this malicious application. Be sure to follow the instructions in the specified order.
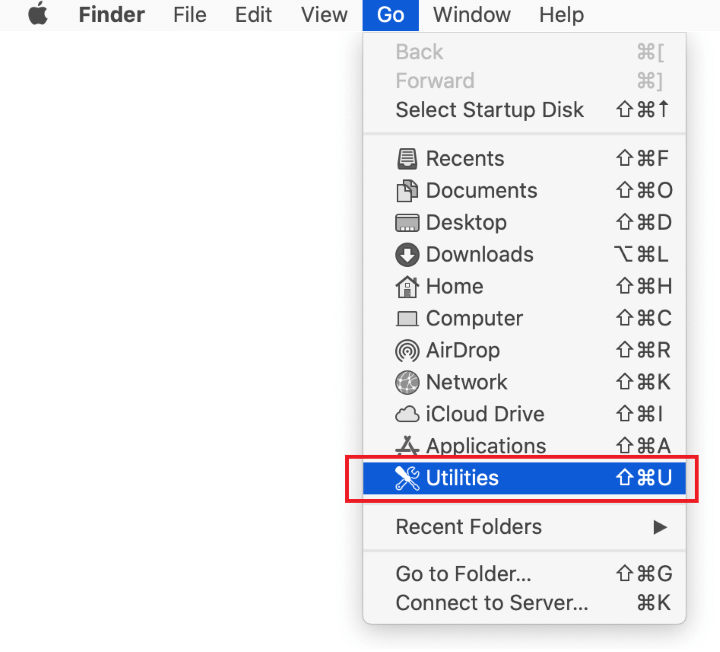
- Expand the Go menu in your Mac’s Finder bar and select Utilities as shown below.

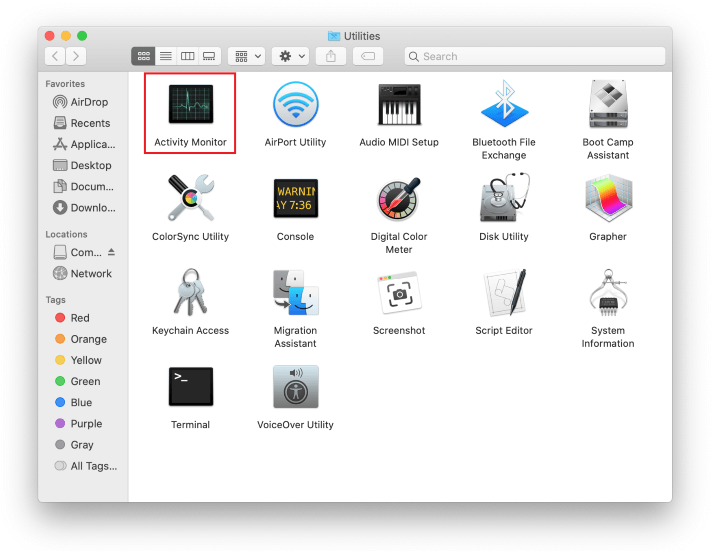
- Locate the Activity Monitor icon on the Utilities screen and double-click on it.

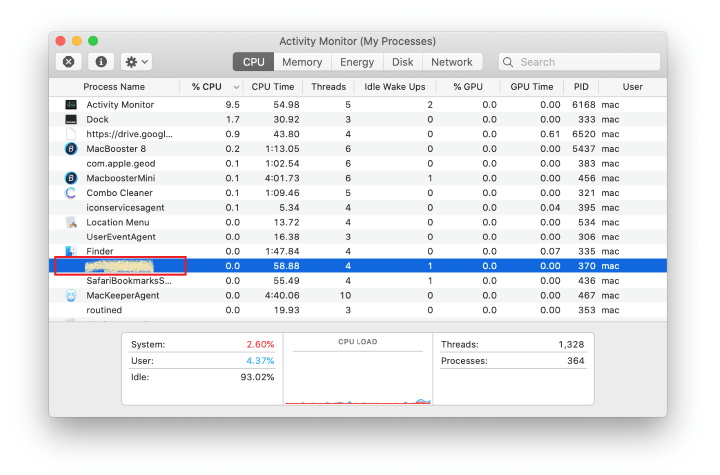
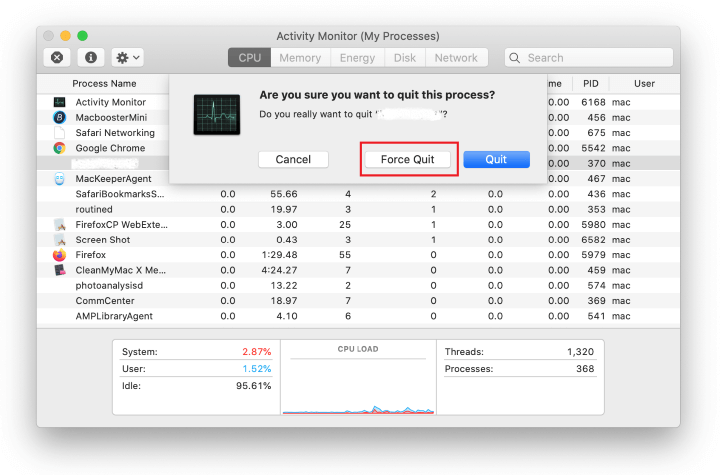
- In the Activity Monitor app, look for a process that appears suspicious. To narrow down your search, focus on unfamiliar resource-intensive entries on the list. Keep in mind that its name isn’t necessarily related to the way the threat is manifesting itself, so you’ll need to trust your own judgement. If you pinpoint the culprit, select it and click on the Stop icon in the upper left-hand corner of the screen.

- When a follow-up dialog pops up asking if you are sure you want to quit the troublemaking process, select the Force Quit option.

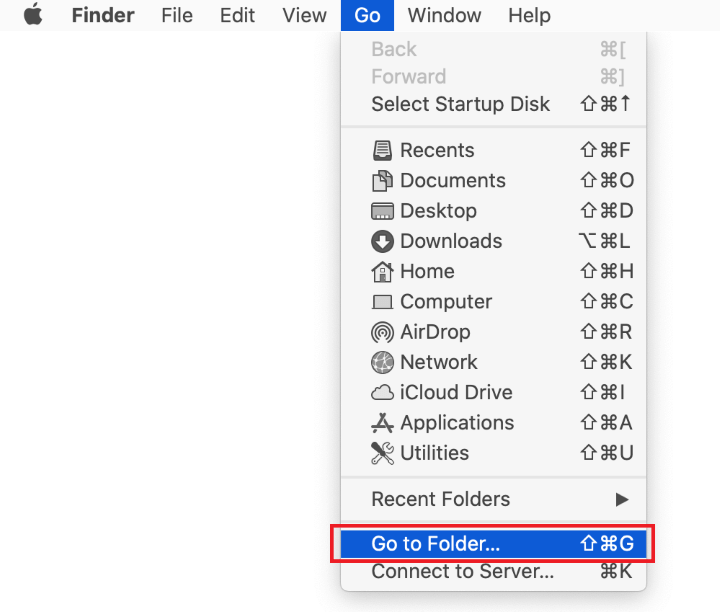
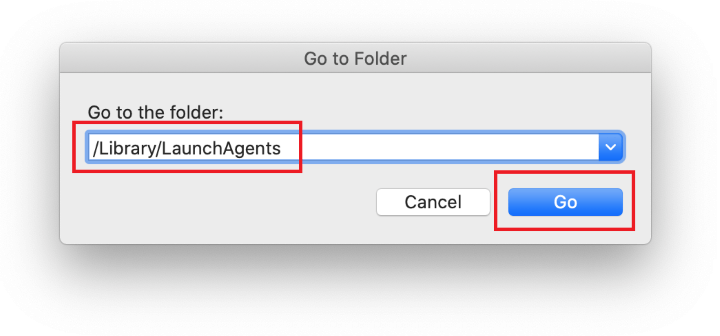
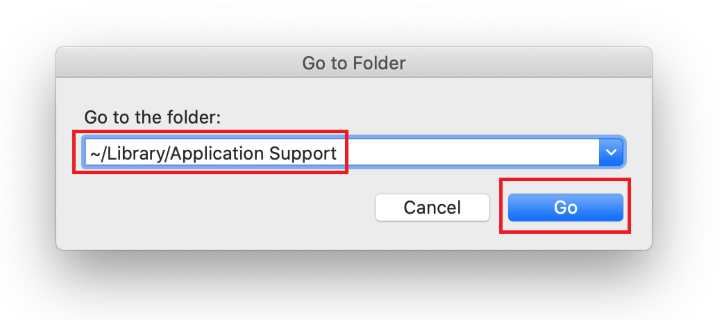
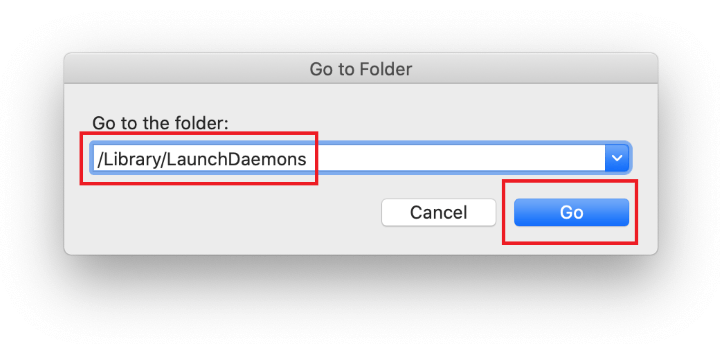
- Click on the Go menu icon in the Finder again and select Go to Folder. You can as well use the Command-Shift-G keyboard shortcut.

- Type /Library/LaunchAgents in the folder search dialog and click on the Go button.

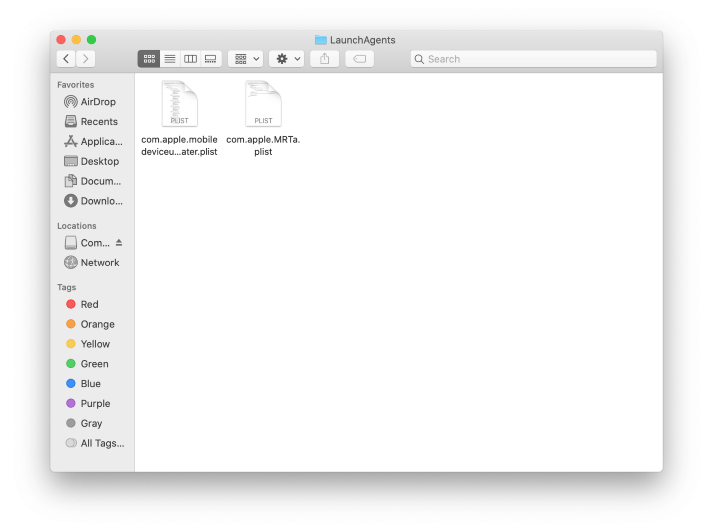
- Examine the contents of the LaunchAgents folder for dubious-looking items. Be advised that the names of files spawned by malware may give no clear clues that they are malicious, so you should look for recently added entities that appear to deviate from the norm.
As an illustration, here are several examples of LaunchAgents related to mainstream Mac infections: com.pcv.hlpramc.plist, com.updater.mcy.plist, com.avickUpd.plist, and com.msp.agent.plist. If you spot files that don’t belong on the list, go ahead and drag them to the Trash.

- Use the Go to Folder lookup feature again to navigate to the folder named ~/Library/Application Support (note the tilde symbol prepended to the path).

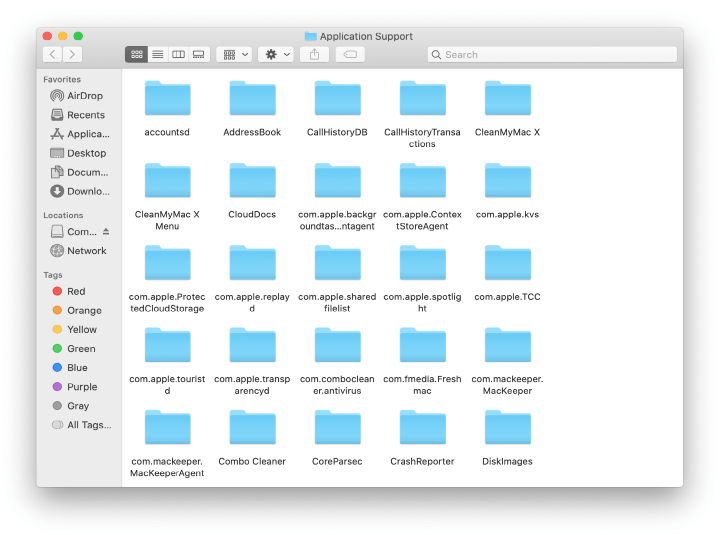
- When the Application Support directory is opened, identify recently generated suspicious folders in it and send them to the Trash. A quick tip is to look for items whose names have nothing to do with Apple products or apps you knowingly installed. A few examples of known-malicious folder names are UtilityParze, ProgressSite, and IdeaShared.

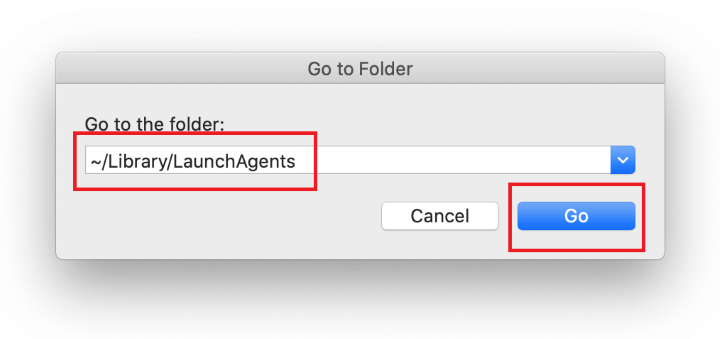
- Enter ~/Library/LaunchAgents string (don’t forget to include the tilde character) in the Go to Folder search area.

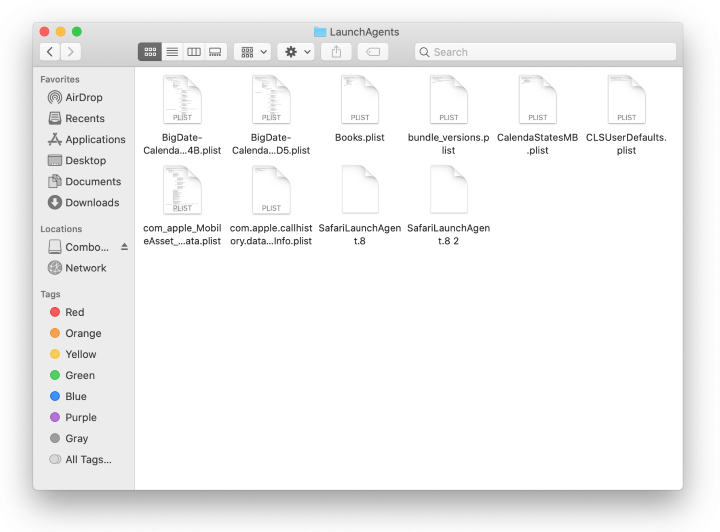
- The system will display LaunchAgents residing in the current user’s Home directory. Look for dodgy items related to “accountsd wants to use the login keychain” pop-up virus (see logic highlighted in subsections above) and drag the suspects to the Trash.

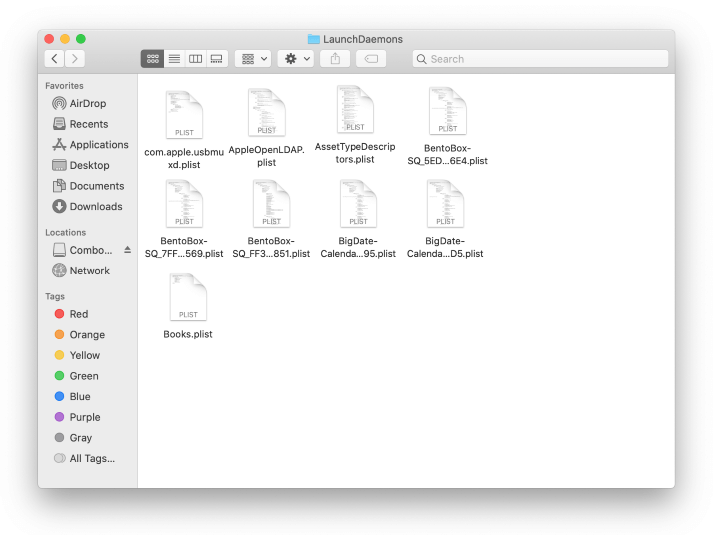
- Type /Library/LaunchDaemons in the Go to Folder search field.

- In the LaunchDaemons path, try to pinpoint the files the malware is using for persistence. Several examples of such items cropped by Mac infections are com.pplauncher.plist, com.startup.plist, and com.ExpertModuleSearchDaemon.plist. Delete the sketchy files immediately.

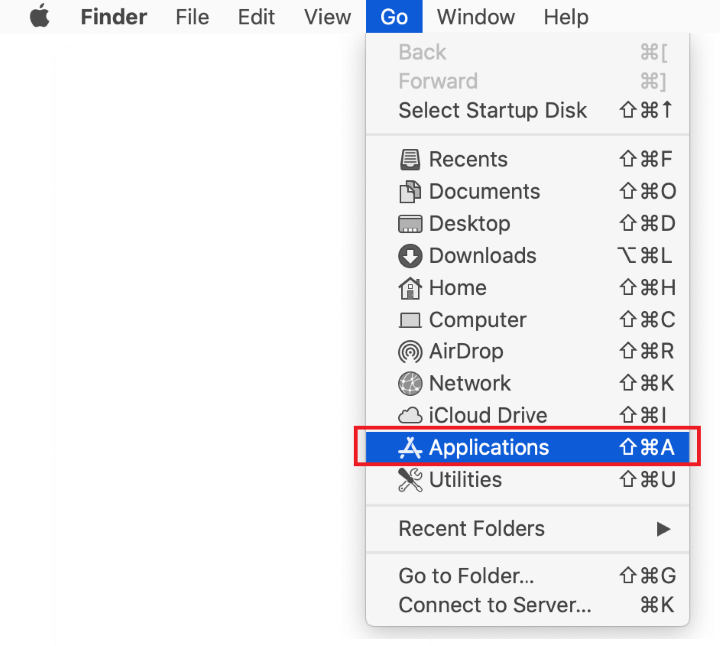
- Click on the Go menu icon in your Mac’s Finder and select Applications on the list.

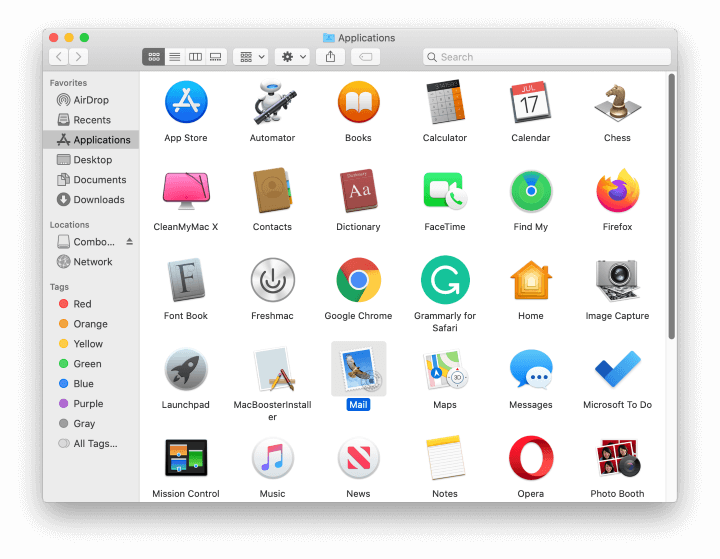
- Find the entry for an app that clearly doesn’t belong there and move it to the Trash. If this action requires your admin password for confirmation, go ahead and enter it.

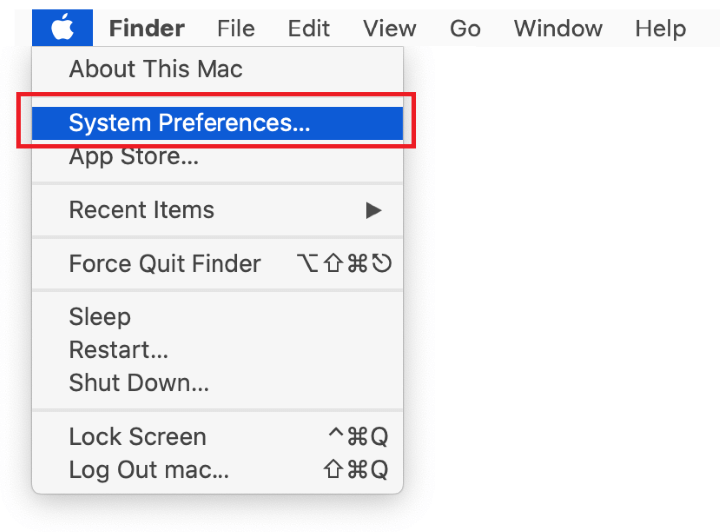
- Expand the Apple menu and select System Preferences.


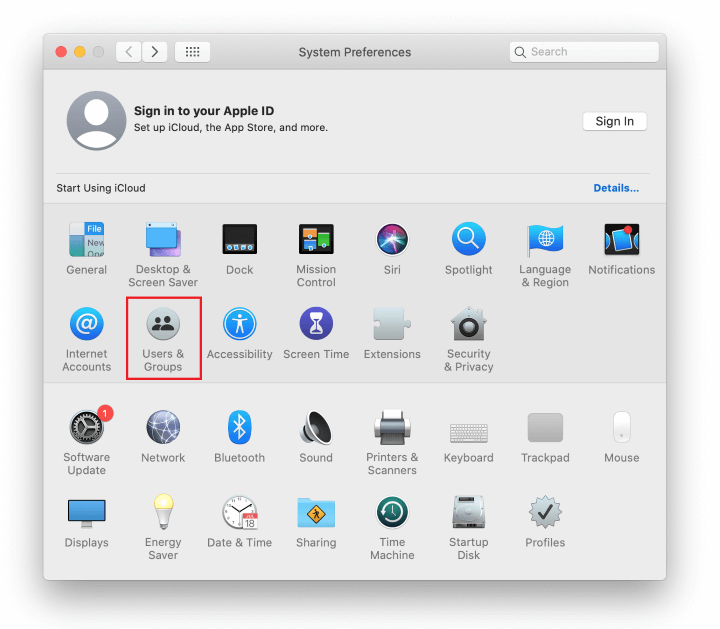
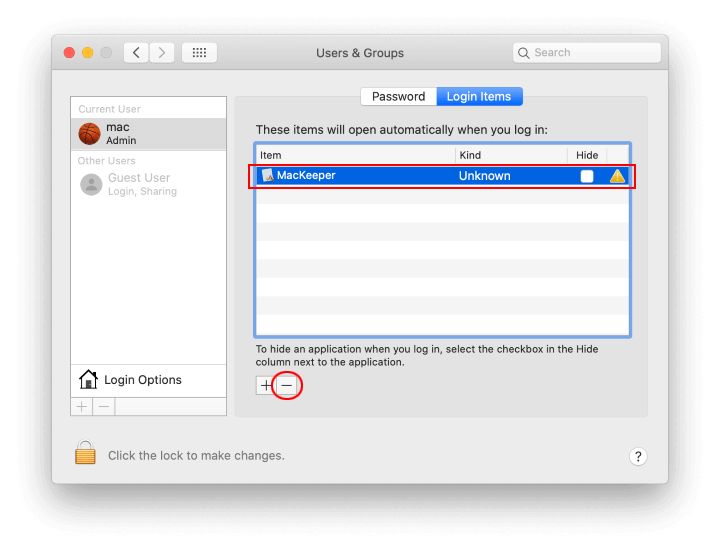
- Proceed to Users & Groups and click on the Login Items tab.
The system will display the list of items launched when the computer is starting up. Locate the potentially unwanted app there and click on the “-” (minus) button.

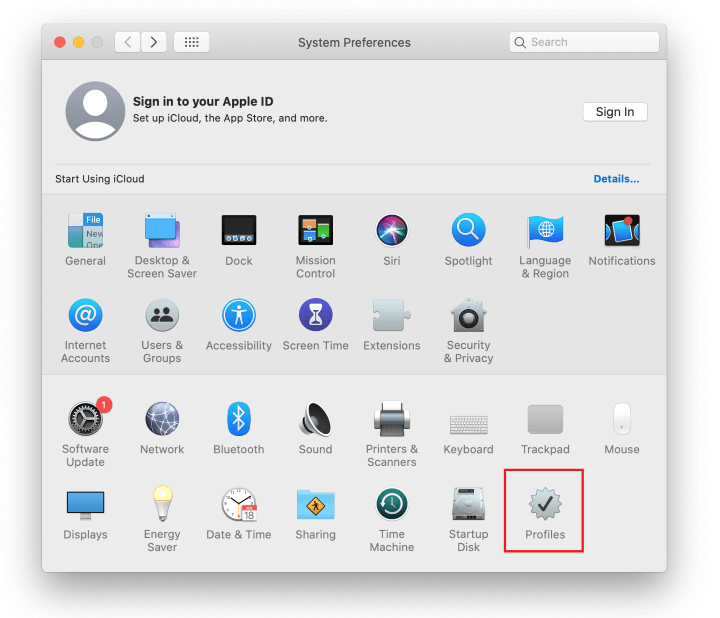
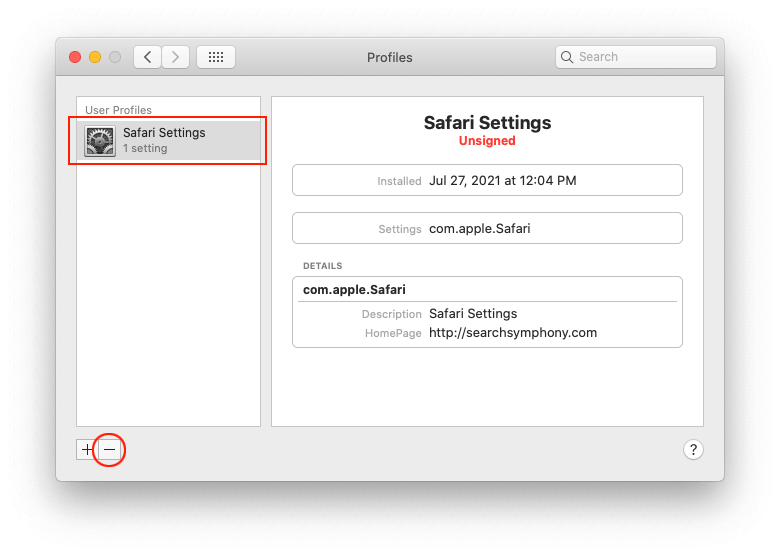
- Now select Profiles under System Preferences. Look for a malicious item in the left-hand sidebar. Several examples of configuration profiles created by Mac adware include TechSignalSearch, MainSearchPlatform, AdminPrefs, and Safari Settings. Select the offending entity and click on the minus sign at the bottom to eliminate it.

If your Mac has been infiltrated by adware, the infection will most likely continue to hold sway over your default web browser even after you remove the underlying application along with its components sprinkled around the system. Use the browser cleanup instructions below to address the remaining consequences of this attack.
Get rid of “accountsd wants to use the login keychain” pop-ups in web browser on Mac
To begin with, the web browser settings taken over by the “accountsd wants to use the login keychain” virus should be restored to their default values. Although this will clear most of your customizations, web surfing history, and all temporary data stored by websites, the malicious interference should be terminated likewise. The overview of the steps for completing this procedure is as follows:
- Remove “accountsd wants to use the login keychain” pop-up virus from Safari
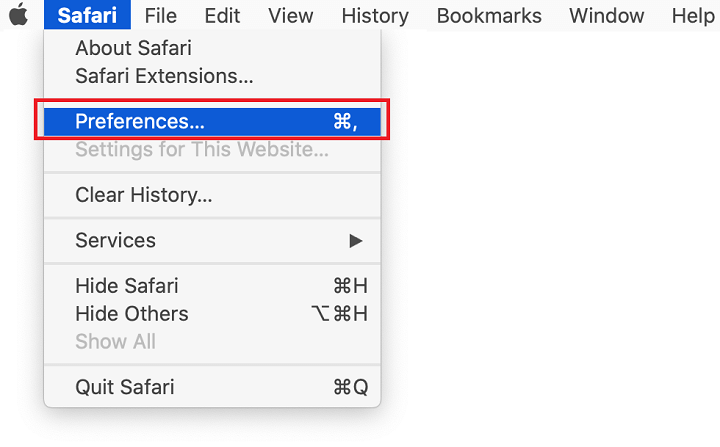
- Open the browser and go to Safari menu. Select Preferences in the drop-down list.

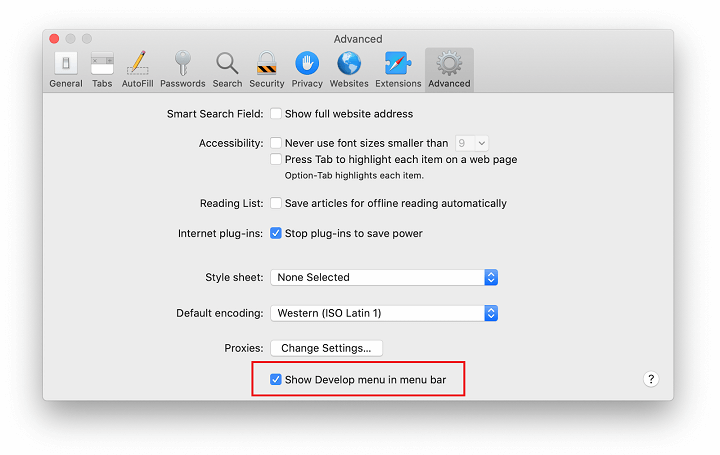
- Once the Preferences screen appears, click on the Advanced tab and enable the option saying “Show Develop menu in menu bar”.

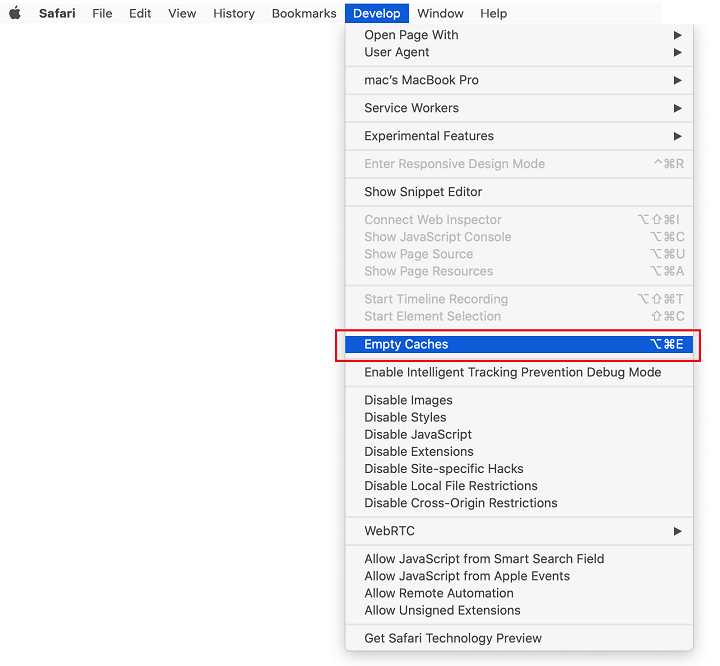
- Now that the Develop entry has been added to the Safari menu, expand it and click on Empty Caches.

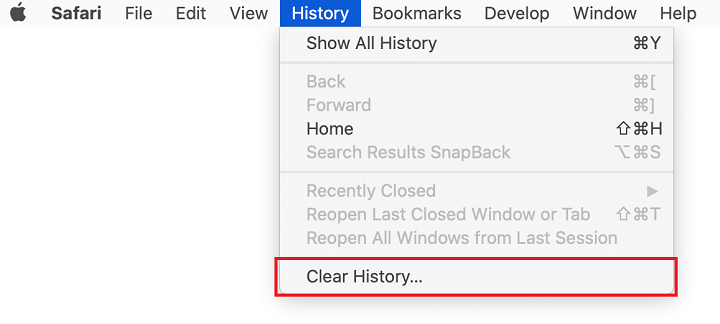
- Now select History in the Safari menu and click on Clear History in the drop-down list.

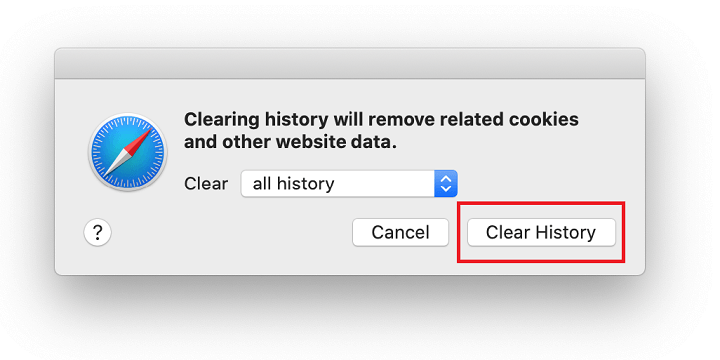
- Safari will display a dialog asking you to specify the period of time this action will apply to. Select all history to ensure a maximum effect. Click on the Clear History button to confirm and exit.

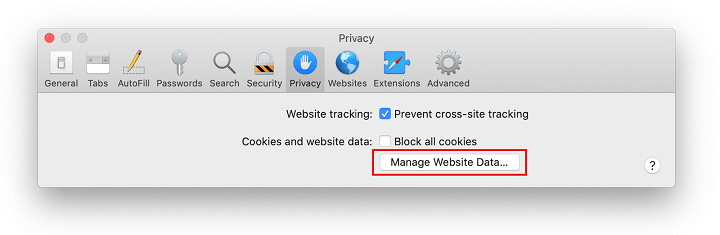
- Go back to the Safari Preferences and hit the Privacy tab at the top. Find the option that says Manage Website Data and click on it.

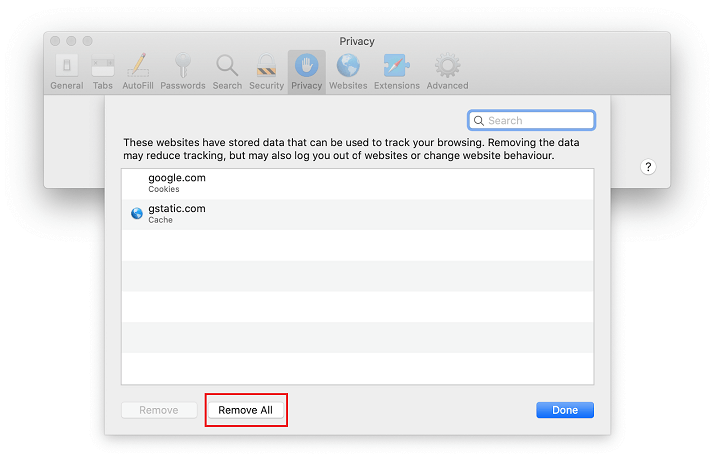
- The browser will display a follow-up screen listing the websites that have stored data about your Internet activities. This dialog additionally includes a brief description of what the removal does: you may be logged out of some services and encounter other changes of website behavior after the procedure. If you’re okay with that, go ahead and click on the Remove All button.

- Restart Safari
- Open the browser and go to Safari menu. Select Preferences in the drop-down list.
- Remove “accountsd wants to use the login keychain” in Google Chrome
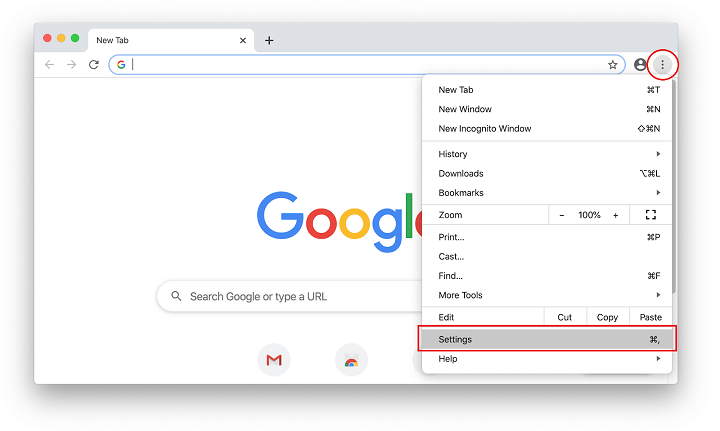
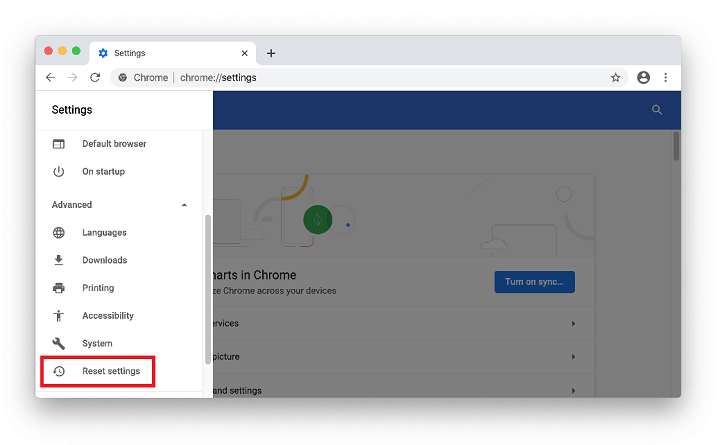
- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down

- When on the Settings pane, select Advanced
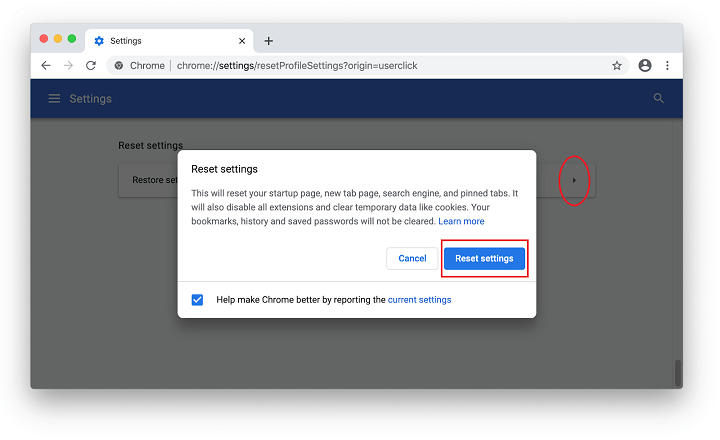
- Scroll down to the Reset settings section.

- Confirm the Chrome reset on a dialog that will pop up. When the procedure is completed, relaunch the browser and check it for malware activity.

- Open Chrome, click the Customize and control Google Chrome (⁝) icon in the top right-hand part of the window, and select Settings in the drop-down
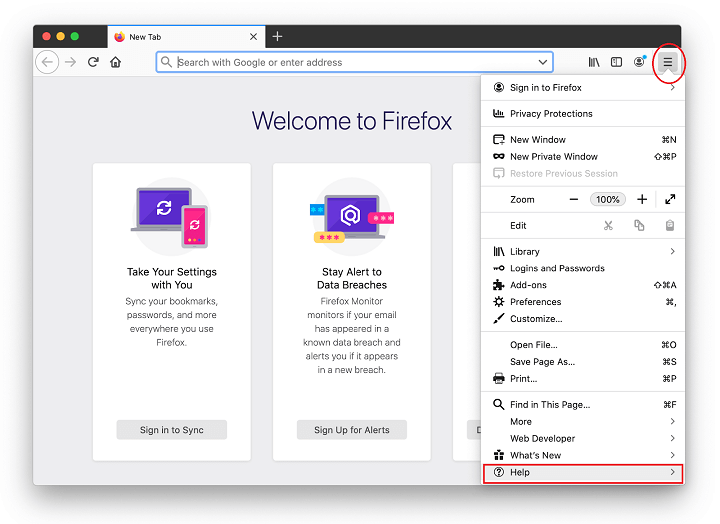
- Remove “accountsd wants to use the login keychain” pop-up from Mozilla Firefox
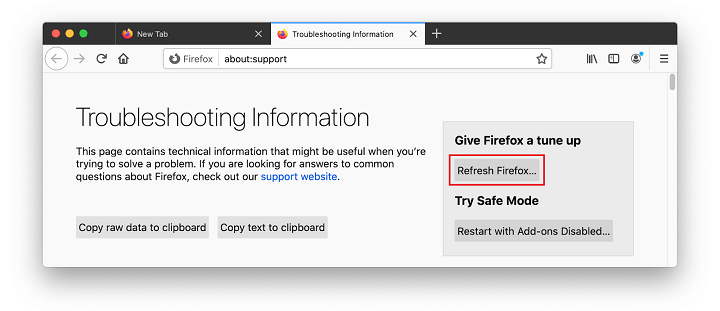
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).


- When on the Troubleshooting Information screen, click on the Refresh Firefox button.

- Confirm the intended changes and restart Firefox.
- Open Firefox and go to Help – Troubleshooting Information (or type about:support in the URL bar and press Enter).
Get rid of “accountsd wants to use the login keychain” pop-up malware using Combo Cleaner removal tool
The Mac maintenance and security app called Combo Cleaner is a one-stop tool to detect and remove “accountsd wants to use the login keychain” virus. This technique has substantial benefits over manual cleanup, because the utility gets hourly virus definition updates and can accurately spot even the newest Mac infections.
Furthermore, the automatic solution will find the core files of the malware deep down the system structure, which might otherwise be a challenge to locate. Here’s a walkthrough to sort out the “accountsd wants to use the login keychain” issue using Combo Cleaner:
- Download Combo Cleaner installer. When done, double-click the combocleaner.dmg file and follow the prompts to install the tool onto your Mac.
By downloading any applications recommended on this website you agree to our Terms and Conditions and Privacy Policy. The free scanner checks whether your Mac is infected. To get rid of malware, you need to purchase the Premium version of Combo Cleaner.
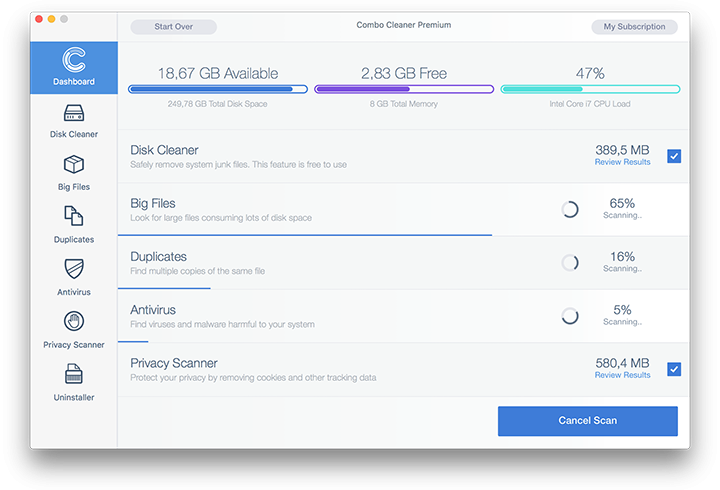
- Open the app from your Launchpad and let it run an update of the malware signature database to make sure it can identify the latest threats.
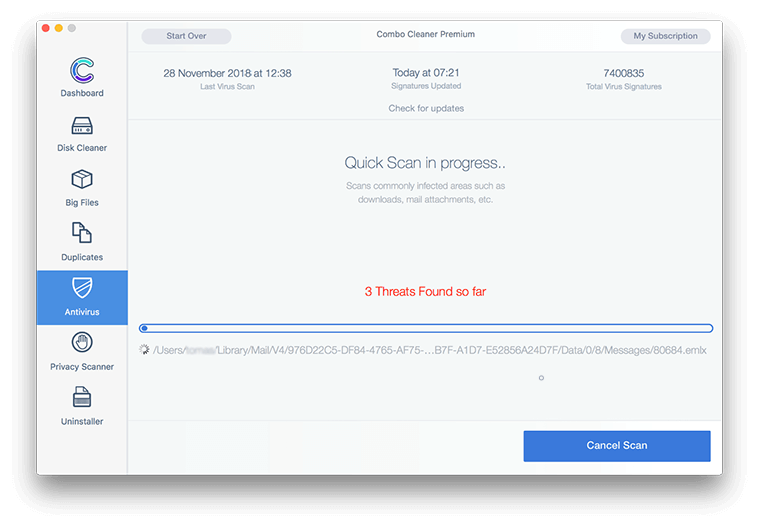
- Click the Start Combo Scan button to check your Mac for malicious activity as well as performance issues.

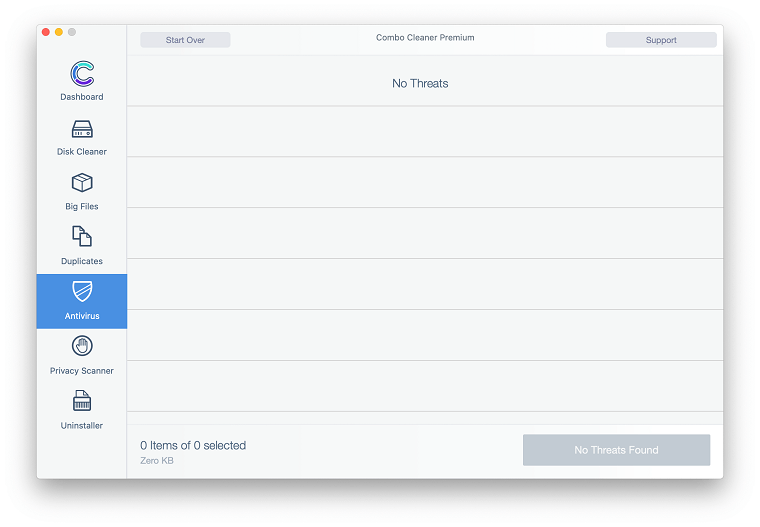
- Examine the scan results. If the report says “No Threats”, then you are on the right track with the manual cleaning and can safely proceed to tidy up the web browser that may continue to act up due to the after-effects of the malware attack (see instructions above).

- In case Combo Cleaner has detected malicious code, click the Remove Selected Items button and have the utility remove “accountsd wants to use the login keychain” threat along with any other viruses, PUPs (potentially unwanted programs), or junk files that don’t belong on your Mac.

- Once you have made doubly sure that the malicious app is uninstalled, the browser-level troubleshooting might still be on your to-do list. If your preferred browser is affected, resort to the previous section of this tutorial to revert to hassle-free web surfing.
FAQ
Accountsd (a portmanteau combining the words “accounts” and “daemon”) is an important system process handling the workflow of authenticating with macOS native and third-party applications that require user credentials to operate. Part of the Accounts Framework, it automatically passes your username and password for a specific program whenever you open it. In plain words, Accountsd saves you the hassle of entering sensitive sign-in details each time you execute an app you have a personal account with. This sort of automation is a great shortcut that facilitates a proper user experience.
Here is the logic behind ensuring that the macOS database of authentication records, or keychain, is in sync with the sign-in data for all the apps you are using: each instance of login to your Mac provides the necessary permissions to programs in one fell swoop. This way, you don’t have to type those details individually for every application.
However, things aren’t always that smooth. One of the common occurrences that throws a spanner in the works is when your Mac repeatedly requests keychain passwords. In the context of the “login” keychain, this drag usually occurs when your system-wide user password and the corresponding keychain password don’t match. Another possible reason for this nuisance scenario is that the “login” keychain may be configured to lock after a certain period of inactivity or when sleep mode is activated. The good news is, both predicaments are easy to sort out through a few tweaks of appropriate settings. The detailed how-to information is provided in the article above.
It depends on the root cause. If you have recently changed your Mac login information, be sure to also update the password for the “login” keychain. To do it, head to “Utilities” from the Mac menu bar, launch the “Keychain Access” app, right-click the “login” entry in the sidebar, and pick the option that says “Change Password for Keychain ‘login’”. Type in the new password and save the change.
If the syncing routine is acting finicky because of a specified lock time-out, you should modify the troublesome setting. Click “Go” in the Apple menu, select “Utilities”, open the Keychain Access app, control-click the “login” item in the left-hand sidebar, and select “Change Settings for Keychain ‘login’”. Then, consider unchecking the “Lock after” setting and also deselecting the “Lock when sleeping” option. Click “Save” so that the new configuration takes effect.
If the recurrent password request mentions the “login” keychain, then there are basically two methods to address the obnoxious issue. One is to ascertain that the Mac user account and keychain passwords are the same. The other is to check if you have any settings that instruct the system to lock the “login” keychain based on certain conditions, for instance, a time interval or a wake from sleep event.
A somewhat different facet of the problem may manifest itself due to general security and privacy settings enabled on your machine. A common example is when macOS is set to require your login password after the sleep mode begins or the screensaver is activated. To see if that’s the case, go to System Preferences (the gear icon in the Dock), select “Security & Privacy”, hit the “General” tab, and take a look at the checkboxes ticked in there. Pay special attention to the “Require password” entry. If you aren’t okay with the current configuration, you might want to deselect the self-explanatory options that are giving you a hard time.
It’s worth mentioning that sometimes such problems kick in after macOS updates. This is because something may have gone wrong during the process and previous user customizations aren’t always retained. Also, password requirements could signal malicious attempts to get hold of sensitive data, and this activity is often precipitated by malware that has cropped up in the computer behind your back. That being said, performing some basic security check-up is a good idea if these requests make you suspicious.